-
Administrator Guide
-
Collect Logs
-
Collect Logs: Apps & Services
- ESXi
- Routers network hardware
- Apple iOS and macOS
- Unix and BSD system logs
- C# and .NET (NLog)
- C# and .NET (log4net)
- Java logback
- Android
- Kubernetes cluster logging with rKubelog
- haproxy
- Advanced Unix logging tips
- Perl
- Windows
- Kubernetes
- Erlang
- Node.js
- Java log4j
- JavaScript
- Unicorn
- PHP
- Docker
- systemd
- Ruby on Rails
- MySQL
- Unix and BSD text log files (remote_syslog2)
- Redis
- Go
- Python
- Elixir
- IIS
- Embedded devices or proprietary systems
-
Collect Logs: Hosting Services
-
Collect Logs: Integrations
-
Manage Logs
- Groups
- Log flood detection
- Web Hooks
- Log colorization
- Linking to logs
- JSON search syntax
- Settings API
- Log destinations
- Alerts
- Command-line client
- Log filtering
- HTTP API
- Automatic S3 archive export
- Managing Senders
- Permanent log archives
- Mapping senders to groups
- Search syntax
- Click-to-search
- Log search API
- Event Viewer
-
Send Logs for Analytics
-
SolarWinds Users & Orgs
-
Support and Security
-
What's New
Automatic S3 archive export
Create an Amazon Web Services account at http://aws.amazon.com and activate Amazon S3 on your account. Once your account is activated, create a bucket for log archives, and share write-only access to Papertrail for nightly uploads.
After setting up S3 archiving it takes approximately 6-7 hours for logs to be available in the archive.
Create and share an S3 Bucket
Create a new bucket for your log archives in your S3 account, using the information below. See Creating, configuring, and working with Amazon S3 buckets in the Amazon documentation for more information.
- Use a unique Bucket Name, such as
companyname-papertrail. The name should consist of only lowercase letters, numbers, and hyphens. (more info). - Assign the bucket to the appropriate region.
- When setting permissions, add access to another AWS account. Add the
user
4b0a516d33d6b490d119301a4b16db3fa49a6b33bdc5135c2ab90e8184f6995fwith Write access enabled for Objects. To set up permissions with IAM instead, see Define Sharing Policy with IAM.
Changes can be made after the fact by selecting the bucket and choosing the Permissions tab.
After submission, Amazon’s management console will change the user name to aws. This is expected.
Amazon also has instructions for editing bucket permissions.
Alternative: Define sharing policy with IAM
If you followed the instructions above to grant permissions via the AWS Management Console, skip this step.
If you prefer defining a bucket policy to control access, here’s an example policy that permits Papertrail to upload archives:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "PapertrailLogArchive",
"Effect": "Allow",
"Principal": {
"AWS": [
"arn:aws:iam::719734659904:root"
]
},
"Action": [
"s3:DeleteObject",
"s3:PutObject"
],
"Resource": [
"arn:aws:s3:::bucket-name/papertrail/logs/*"
]
}
]
}where bucket-name/papertrail/logs/ is the directory for Papertrail. The s3:DeleteObject action isn’t strictly necessary – it’s only used to clean up the temporary test_file.txt during initial configuration. (However, since s3:PutObject also permits overwrites, denying s3:DeleteObject doesn’t provide any significant protection.)
Tell Papertrail the bucket name
Under Settings > Archives, enable S3 archive copies and provide the S3 bucket name.
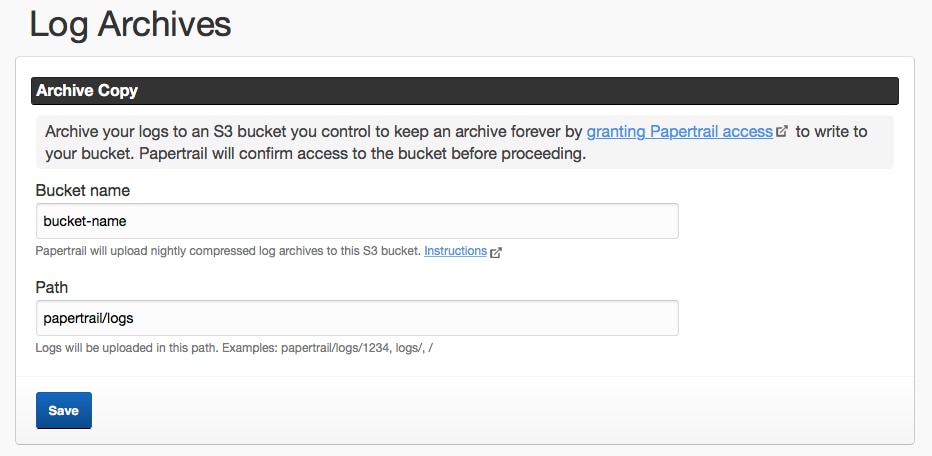
Papertrail will perform a test upload as part of saving the bucket name (and will then delete the test file). Note that a new bucket can sometimes take several hours to become available, due to DNS propagation delays. If it fails, wait two hours, and try again.
When archives are uploaded to the bucket, each file is named under the path (key prefix) provided to Papertrail, typically papertrail/logs/<xxx> where <xxx> is an ID. For example, an archive file for 3 PM UTC created on February 25, 2019 would be:
bucket-name/papertrail/logs/54321/dt=2019-02-25/2019-02-25-03.tsv.gzDays are from midnight to midnight UTC.
Questions
Why does Papertrail support S3 but not Glacier?
Papertrail supports S3 rather than Glacier because:
- AWS offers the ability to trickle files from S3 to Glacier using a policy that you define, so by supporting S3, Glacier is automatically a possible destination. Visit S3 Object Lifecycle Management.
- Archived log files compress extremely well, often 15:1 or more, so the total cost of archived logs stored in S3 is extremely small (often pennies per month). Storing a long-term log archive in your S3 bucket will almost always cost less than 1% of the total cost of Papertrail. There’s effectively no cost savings.
Are Archives Encrypted at Rest?
Yes, Papertrail takes advantage of S3’s server-side encryption so that archived data is encrypted at rest using AES-256.
The scripts are not supported under any SolarWinds support program or service. The scripts are provided AS IS without warranty of any kind. SolarWinds further disclaims all warranties including, without limitation, any implied warranties of merchantability or of fitness for a particular purpose. The risk arising out of the use or performance of the scripts and documentation stays with you. In no event shall SolarWinds or anyone else involved in the creation, production, or delivery of the scripts be liable for any damages whatsoever (including, without limitation, damages for loss of business profits, business interruption, loss of business information, or other pecuniary loss) arising out of the use of or inability to use the scripts or documentation.