Last updated: October 2025
Logs are a ubiquitous component of IT. They come in all shapes and sizes from a wide variety of sources and possible destinations. But at the end of the day, all types of logging serve a fundamental role in a technological infrastructure: they allow a system to record information about its behavior to a persistent medium. People can then review this information and reconstruct what happened, allowing them to detect and address any issues they may find.
What are logs?
Logs are records of events within an operating system, application, or service. They contain valuable information about the operation of these systems, including errors, warnings, and informational events. Logs are essential for troubleshooting, diagnosing problems, and understanding system behavior over time.
In this post, you’ll learn some basic and more advanced techniques to filter your events and make them more manageable.
Windows Event Viewer and How You Access It
Windows Event Viewer is a powerful tool for system administrators and power users. It helps you monitor and troubleshoot your Windows operating system. By reviewing event logs, you can diagnose system errors, security issues, and application problems.
What is Windows Event Viewer?
Windows Event Viewer records significant events on your computer. These events can include:
- System warnings and errors
- Application crashes
- Security events
Event Viewer categorizes these events into different logs. The most commonly used logs are:
- Application log: Records events logged by applications.
- System log: Records events logged by Windows system components.
- Security log: Records security-related events, such as login attempts.
How to access Windows Event Viewer
Accessing Windows Event Viewer is simple. Follow these steps:
- Using the Start Menu
- Click on the Start button or press the Windows key.
- Type “Event Viewer” in the search bar.
- Click on Event Viewer from the search results.
- Using the Run Dialog
- Press Windows + R to open the Run dialog box.
- Type
eventvwr.mscand press Enter.
- Using Control Panel
- Open the Control Panel.
- Navigate to System and Security.
- Click on Administrative Tools.
- Double-click on Event Viewer.
Why do we need to filter logs?
Filtering logs allows IT professionals to focus on the most relevant information, making it easier to identify and troubleshoot issues. By filtering logs, users can reduce the noise and extract actionable insights from the vast amount of data generated by their systems.
Log filtering techniques
Let’s start by covering some basic filtering options. Instead of showing you every possible option, I’ll cover the main ones so you can get a sense of the overall approach. With the basic options out of the way, we can continue to more advanced ones.
Filtering by event time
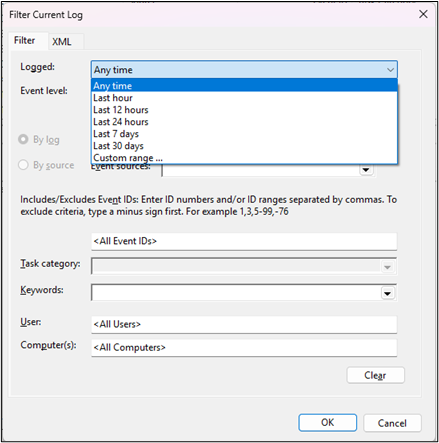
With the Event View window open, expand the Windows Logs option. Then, right-click Application and click on Filter Current Log.
In the newly opened window, you’ll see options you can use to filter the log. The first option is Logged, which refers to the time stamp for the event. Clicking the combo box next to the label allows you to see the existing options for this field:
- Any time
- Last hour
- Last 12 hours
- Last 24 hours
- Last 7 days
- Last 30 days
- Custom range…
Most of the options are self-explanatory. However, let’s look at Custom range. Click on it. You’ll see a new window like this:
You’ll notice you can’t choose the date and time for the filter. To be able to select the date and time for the “From” time stamp, click on the first combo box and change it to “Event On.” You can also do the same for the second timestamp.
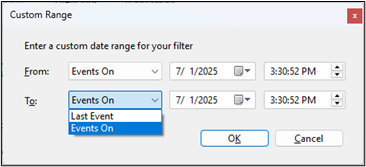
After configuring the dates to your needs, click OK. Then go back to the previous screen, click OK, and the filtering will occur.
Filtering by event level
Now, let’s filter by event level. Go back to the Event Viewer home screen, expand the Windows option again, and right-click one of the logs found there. Then, click Filter Current Log.
Immediately after the options for filtering by time, you’ll see several boxes referring to event levels. You can check how many levels you want to filter by:
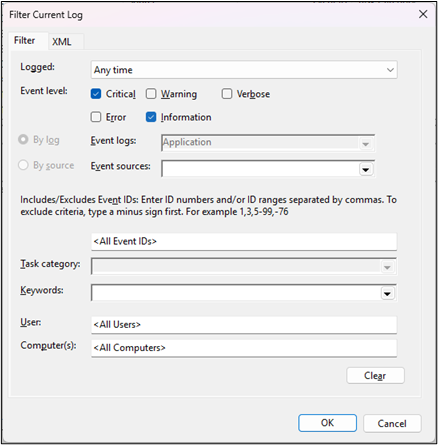
When you’re ready, click OK, and the filtering will take place.
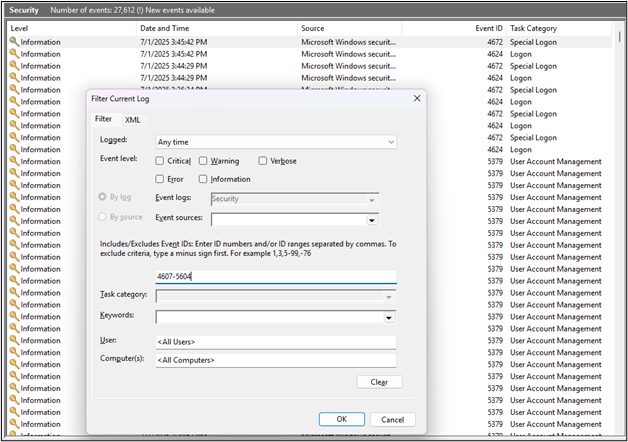
Filtering by event IDs
Before covering more advanced techniques, I’ll share a final tip. You can easily include or exclude event IDs. You have to enter IDs separated by commas. To exclude a given ID, start with a minus sign. Ranges also work: you can use a minus sign to separate the first ID from the last.
Both sides are inclusive, as you can see from the following example:
Advanced Log Filtering
With the basic filtering techniques out of the way, let’s focus on more advanced ones.
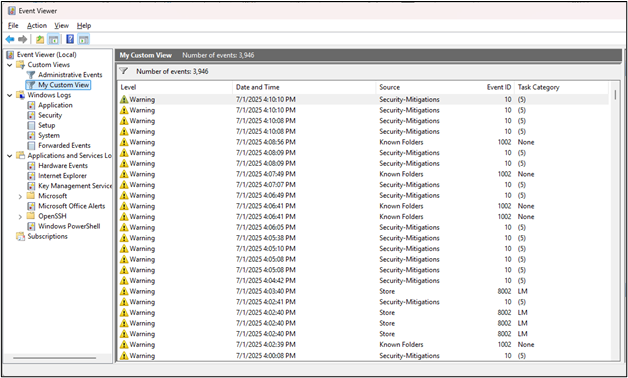
Using custom views
The filtering capabilities we’ve discussed so far may be sufficient for basic filtering needs, but they have limitations. If you have more advanced filtering needs, you need custom views. Custom views enable you to use only the information you need, combining events from different logs or sources.
On the Event Viewer window, right-click Custom Views and then click Create Custom View.
For this example, these are the settings I’m picking:
- Logged: last 7 days
- Event level: critical and warning
- Event logs: application, security
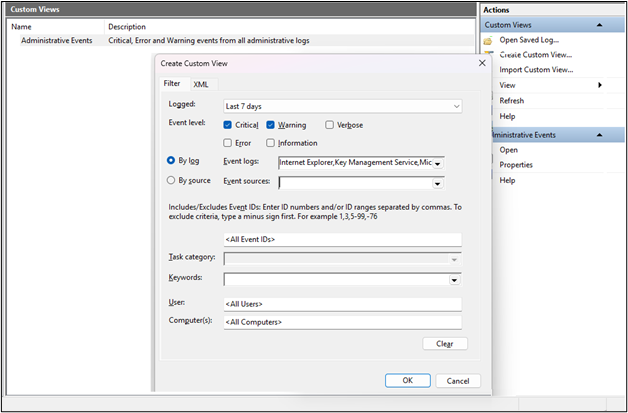
I’ll leave the remaining options with their default values. After clicking OK, this is what you should see:
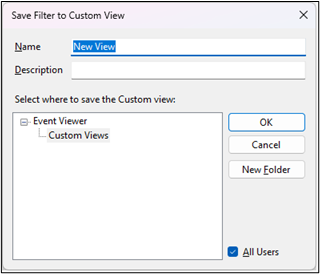
For the name, I’ll use “My Custom View”, and I’ll leave the description blank. After you’re done, click OK, and you should see your brand-new custom view:
Using XML Filtering
The custom view you’ve just created is already an improvement over the basic filtering capabilities. However, we can take it even further. Let’s examine how we can utilize XML querying for more effective filtering.
We’ll start by creating a new custom view. Repeat the process from the previous section: go to the Event Viewer window, right-click Custom Views, and click Create Custom View.
Here’s where things change. Instead of doing what you did the previous time, go to the XML tab and check the Edit query manually box in the lower-left corner of the window:

After you click this checkbox, you’ll be prompted with the following message:
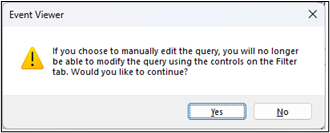
Click Yes. You’ll then be allowed to write a filter using XML’s XPath syntax. Copy the following excerpt of code and paste it in the window:
<QueryList>
<Query Id="0">
<Select Path="Security">
*[EventData[Data[@Name='SubjectUserName'] and (Data='testuser')]]
</Select>
</Query>
</QueryList>Don’t forget, of course, to change “testuser” to an actual user name, keeping the quotes. Click OK and enter a name and a description for your custom view. Finally, click OK, and your newly created custom view will be added to the list, and you’ll be able to see its results.
Conclusion
Logs are a unique window into the depths of your technological infrastructure. Windows logs are no exception, but they can sometimes be frightening. It’s essential to have a way of making Windows events more manageable. Filtering your events is one way to do so. By using the filtering techniques described in this post, you’ll be able to find the information you need according to your criteria quickly.
However, even after learning and putting the tips we’ve shared today into practice, you may still feel like you’re spending too much time on Windows event logs. If this is the case, the next logical step is to consider the tools at your disposal and find one capable of handling both Windows event logs and logs from other systems. Consolidating your log data in a single log management system can make your life much easier by simplifying and reducing the time spent on troubleshooting, allowing you to focus on the work that generates the most value for your organization.
One tool you may want to consider is SolarWinds Papertrail. SolarWinds Papertrail is a cloud-based log tool, and it’s quick to set up and easy to use. It can centralize logs from a massive variety of sources, including Windows event logs. It aggregates your log data and lets you search multiple sources from a single search bar. With its “live tail” function, you can even search and view real-time log data, which is particularly useful when troubleshooting and testing issue resolution. Want to give it a try? You can sign up for a free trial of SolarWinds Papertrail now and see just how it can work for you.
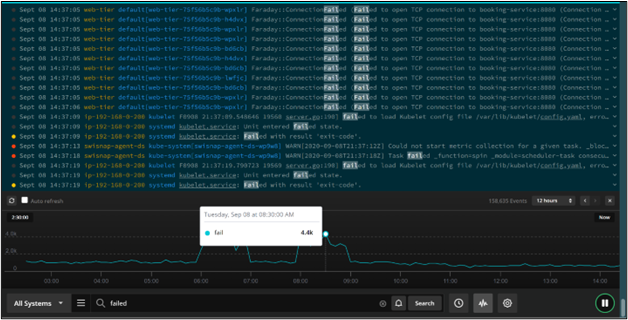
For a more comprehensive view of system performance, consider SolarWinds Observability SaaS. SolarWinds Observability provides holistic observability across on-premise, hybrid, and cloud-native applications and infrastructure. Connecting data points from across your environment to deliver business insights and operational intelligence, SolarWinds Observability SaaS enables you to identify and resolve issues quickly.
—
This post was written by Carlos Schults. Carlos is a .NET software developer with experience in desktop and web development, and he’s now trying his hand at mobile. He has a passion for writing clean and concise code, and he’s interested in practices capable of helping you improve app health, such as code review, automated testing, and continuous build.