Tips from the Team
By engineers, for engineers
At SolarWinds Papertrail we are software engineers who are passionate about programming, debugging, logging and pretty much everything about building and running applications. We enjoy keeping our coding skills sharp and playing with new technologies. Below are some of things we have picked up along the way.
Fully Functional for 30 Days
Kubernetes Observability 101
Kubectl Logs: How to Tail Logs in Kubernetes
Logging in Docker – How to Get It Right
HAProxy Logging – How to Tune Timeouts for Performance
Kubernetes Logging: Tips to Avoid Memory and Resource Issues
Centralized Logging for .NET 5 Applications
Heroku: Most Common Errors Explained
Azure Web Apps Logging With Net 5—How-To
7 Problems to Look out for When Analyzing Garbage Collection Logs
Logging in Java – Best Practices and Tips
Kubernetes Observability 101
In the landscape of containerized applications, Kubernetes has emerged as the de facto orchestration tool. However, effectively managing a Kubernetes environment demands a deep understanding of observability. In this article, we’ll dive into Kubernetes observability, distinguishing it from traditional monitoring, and discuss its significance, challenges it addresses, popular tools, and how to choose the right tool for your needs.
Kubectl Logs: How to Tail Logs in Kubernetes
There are times when you need to see what’s happening with your applications in Kubernetes quickly. For this, reading the most recent log lines is the most immediate thought you might have. Fortunately, a quick way to troubleshoot and explore logs is to use the kubectl logs command. With kubectl logs, you can even read logs as they’re generated and focus only on the most recent ones. You can also read logs from all containers in a pod or a deployment.
In this post, I’ll show you different ways of reading logs from your application using the command line tool. We’ll teach you how to tail the logs—or read the most recent log lines—with a few common scenarios. Before we dive in, let me start by covering a few basic concepts.
Logging in Docker – How to Get It Right
Last updated: February 26, 2024
Life would be much simpler if applications running inside containers always behaved correctly. Unfortunately, as every sysadmin and developer knows, that is never the case. When things inevitably start going wrong you need diagnostic information to figure out how and why. Being able to gather useful information from your Docker container logs can mean the difference between a minor issue and a critical outage.
HAProxy Logging – How to Tune Timeouts for Performance
Last updated: October 2025
HAProxy (high availability proxy) is a critical part of modern systems infrastructure. It’s ideally the first point of contact for users who access your application. When configured correctly, HAProxy significantly improves your app’s performance. Through load balancing, HAProxy ensures that each service your application depends on remains accessible to users, particularly under load conditions that would otherwise impact application performance.
Kubernetes Logging: Tips to Avoid Memory and Resource Issues
Last updated: October 10, 2025
Containerization has simplified the life of the developer. It allowed developers to offload the setup of the necessary runtimes, libraries, and servers. For small projects, this was all that developers needed. However, managing multiple containers for larger and more complex applications became difficult. Kubernetes emerged to address this problem, simplifying complex deployments through the use of orchestration.
Although Kubernetes is an excellent tool, it also introduces new challenges, such as memory usage issues. In this post, we’ll explore how to utilize logging efficiently, enabling you to identify and avoid common problems with misconfigured resource allocation in Kubernetes.
Centralized Logging for .NET 5 Applications
Last updated: February 1, 2024
.NET 5 is a shifting point for the .NET ecosystem, bringing Mono, Xamarin, and .NET development into a single codebase. Almost a year later, however, there’s still some confusion lingering, especially when it comes to migrating your old apps.
Heroku: Most Common Errors Explained
Last updated: January 22, 2024
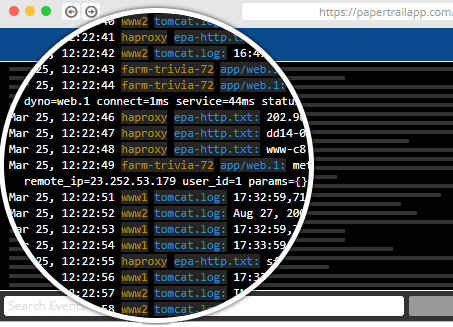
The allure of quickly spinning up an app on a platform as a service (PaaS) instead of cobbling together a solution on an infrastructure as a service (IaaS) makes Heroku an appealing option for many developers. With the explosive growth in the platform as a service market, new features and capabilities are continually rolling out. Along with the fast-paced evolution of Heroku comes an increase in complexity, which can create challenges for application developers.
Azure Web Apps Logging With Net 5—How-To
Last updated: January 22, 2024
Logging is an essential part of any application, no matter the tech stack or service to which you deploy. When things go wrong in production, logging might just save you from going blind when trying to fix the issue.
In this post, you’ll see how to implement logging for your .NET 5 Asp.NET app on Azure Web Apps.
7 Problems to Look out for When Analyzing Garbage Collection Logs
Last updated: October 13, 2025
Modern garbage collectors use sophisticated algorithms to manage unused memory, so you don’t have to. But when things aren’t working right, you need a way to peek under the hood and troubleshoot issues. Analyzing garbage collection (GC) logs can provide key insights into the behavior and performance of programming languages using automatic memory management, such as Java. If you suspect you’ve got a memory problem with your Java app, the GC log is the first place to look.
Logging in Java – Best Practices and Tips
Last updated: October 2025
Robust application logging is central to any quality strategy. Unfortunately, many quality strategies fall short, implementing logging in a less-than-stellar way. Java application logging is no different. And since we’re discussing one of the most popular programming languages, investments in enhancing the overall Java logging strategy could yield significant dividends in the future.